In the world of Internet of Things (IoT) and single-board computer, the Raspberry Pi stands apart as a flexible and affordable service for various jobs. One critical facet of taking care of these jobs is developing efficient remote access to the Raspberry Pi, allowing customers to check and control their IoT devices from throughout the world. The amalgamation of IoT monitoring and remote peer-to-peer (P2P) Virtual Private Cloud (VPC) connectivity has actually come to be an essential method for fanatics and professionals alike.
The requirement for remote accessibility to IoT tools has actually ended up being progressively noticeable as the IoT community proceeds to broaden. Checking the status of IoT tools in real-time has become an essential need for efficient administration.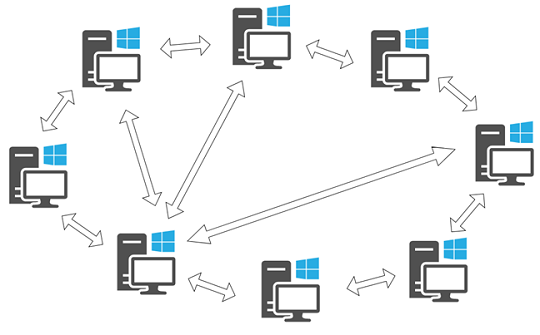
IoT Security Essentials: Safeguarding Your Devices with Remote Access
Making sure the protection of remote access to IoT gadgets is paramount. It develops a safe and secure communication channel over an insecure network, making it an excellent option for from another location keeping an eye on and managing IoT devices.
The convergence of remote accessibility and IoT monitoring has resulted in cutting-edge services that allow users to keep an attentive eye on the condition of their devices. Remote monitoring of IoT tools has become much more sophisticated, enabling users to collect insights right into efficiency metrics, receive notifies for abnormalities, and even carry out remote diagnostics. This level of control is specifically important for applications where IoT gadgets are released in remote or hard to reach locations.
Peer-to-peer (P2P) connectivity in the context of IoT has gotten traction as it provides a straight communication web link between gadgets without the demand for intermediaries. P2P IoT services make it possible for effective data exchange between gadgets, enhancing the general responsiveness of the system. Combining P2P connectivity with a Virtual Private Cloud (VPC) design ensures a private and separated network setting, adding an extra layer of security to remote gain access to.
The idea of securely accessing IoT devices prolongs past Raspberry Pi to encompass a broad array of tools that constitute the IoT community. Whether it’s sensors, actuators, or other IoT parts, establishing a safe and secure connection is crucial for keeping the stability and discretion of the transmitted information. Safe and secure access protocols, such as SSH, play an essential role in accomplishing this objective, guaranteeing that only accredited individuals can interact with and keep an eye on IoT tools remotely.
The assimilation of SSH right into the remote accessibility structure for IoT gadgets enables individuals to from another location keep an eye on Raspberry Pi gadgets also when they are located behind firewalls. This is particularly critical for scenarios where IoT gadgets are deployed within business networks or personal atmospheres with stringent safety measures. SSH’s capability to traverse firewall softwares securely makes it an indispensable device for managing IoT infrastructure in varied and difficult network atmospheres.
For added insights on optimizing remote accessibility to Raspberry Pi and enhancing IoT tool tracking, look into remote ssh iot
Securely Connect and Monitor Raspberry Pi: A Deep Dive into Remote SSH for IoT
Peer-to-peer (P2P) connections within a Virtual Private Cloud (VPC) for IoT present an unique measurement to remote access services. This method not just makes sure direct connectivity but additionally offers a scalable and separated network setting for IoT gadgets. The mix of P2P and VPC addresses typical obstacles associated with standard remote gain access to approaches, using an extra robust and adaptable solution for securely attaching and checking IoT tools.
In conclusion, the landscape of remote accessibility to IoT tools, specifically Raspberry Pi, has actually advanced to encompass innovative solutions that prioritize security, performance, and scalability. The combinations of IoT surveillance, remote P2P VPC connection, and protected accessibility procedures like SSH has propelled the abilities of fanatics and professionals in handling their IoT projects. As the IoT ecosystem remains to broaden, the importance of trusted and protected remote accessibility services will just come to be much more noticable, driving additional innovation in this vibrant area.
